
























लगातार बच्चों के मरने की खबर समाने आ रही है | कभी स्कूल बस का Accident हो जाता तो कभी स्कूल के ऑटो का एक्सीडेंट हो...
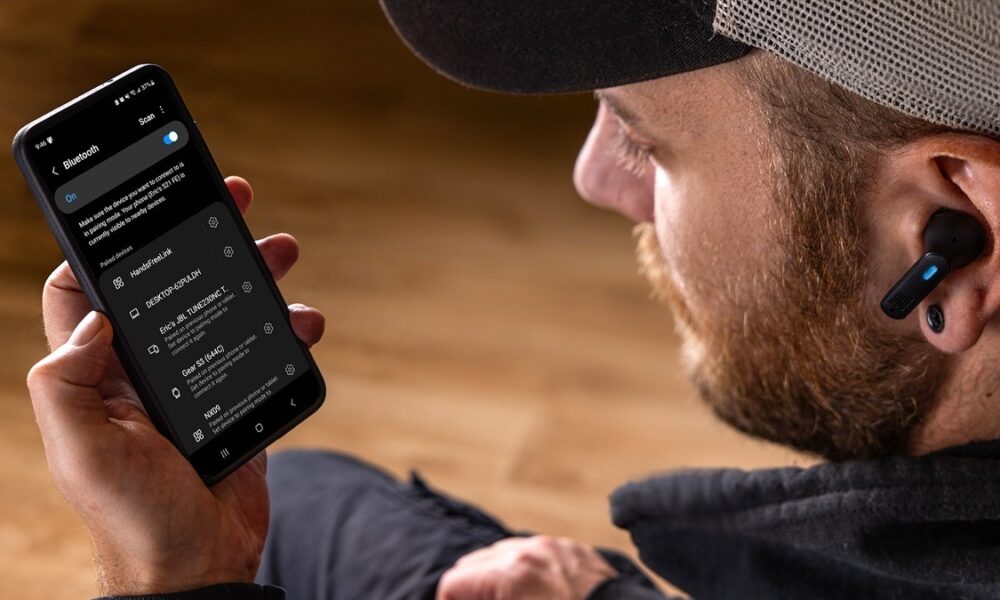


जैसे-जैसे समय बदल रहा है वैसे वैसे लोगो की पसंद भी बदल रही है | बात की जाए Technology की तो ये इंसान की ज़िंदगी का...



भारत में अगर किसी वाहन की मांग है तो वो है Electric Vehicles की | लगातार Electric Vehicles (EV) की मांग बढ़ती जा रही है। इसमें...



अगस्त 2019 के बाद यह पहली बार है जब PM ने राज्य का दर्जा बहाल करने का उल्लेख किया है; नवरात्रि के दौरान मांसाहारी भोजन के...



हाल में PM Narendra Modi देश के पहले Digital content creators अवार्ड में कई सारे creators से मिलने और उन्हें सम्मानित किया | PM मोदी माइक्रोसॉफ्ट...



Uttar Pradesh में उस वक्त सनसनी फैल गई जब एक सुन सान जगा पर 7 महीने के बच्चे की रोने की आवाज़ सुनाई देती है जब...



Punjab के Ludhiana में उस वक्त सनसनी फैल गई जब एक व्यक्ति की टुकड़े की हुई शव बरामद हुआ है। गश्त के दौरान रेलवे कर्मचारी को...


Uttarakhand के Rishikesh में एक बड़ी जनसभा को संबोधित करते हुए PM Narinder Modi ने पिछली Congress सरकारों पर तीखा हमला बोला| उन्होंने कहा कि जब...



Tamil Nadu से दिल दहला देने वाला वीडियो सामने आया है | जहां एक कार के साथ भयानक हादसा हो गया और इस हादसे में 6...



ड्राइवर नशे की हालत में था और जब बस उनहानी गांव के पास पहुंची तो उसने अपना संतुलन खो दिया वे जिस बस में सवार थे,...